Supply Chain
Fix the dependencies that actually matter. Find vulnerable and malicious dependencies, understand what's reachable and exploitable in your environment, and remediate them autonomously.
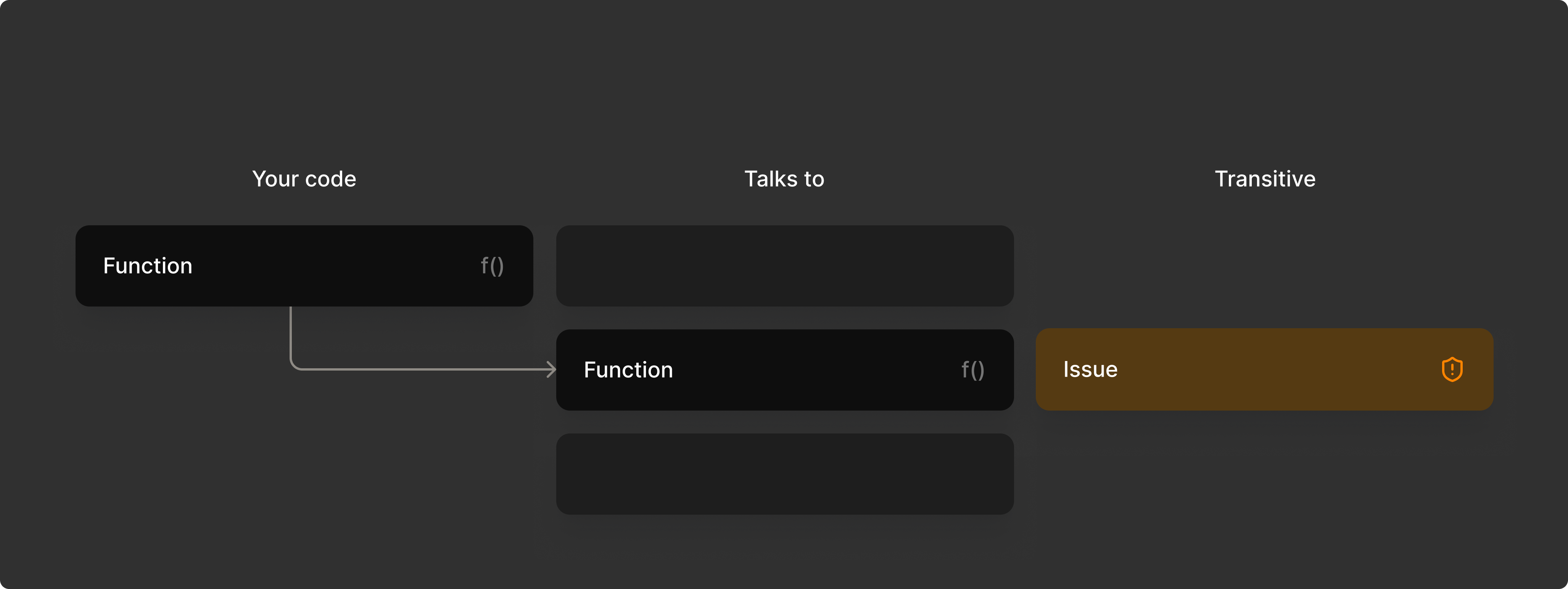
Determine whether a dependency is actually exploitable
depthfirst traces execution paths from your code, through the full transitive dependency tree, down to the vulnerable function or symbol, so teams can focus on the issues their application can actually reach.
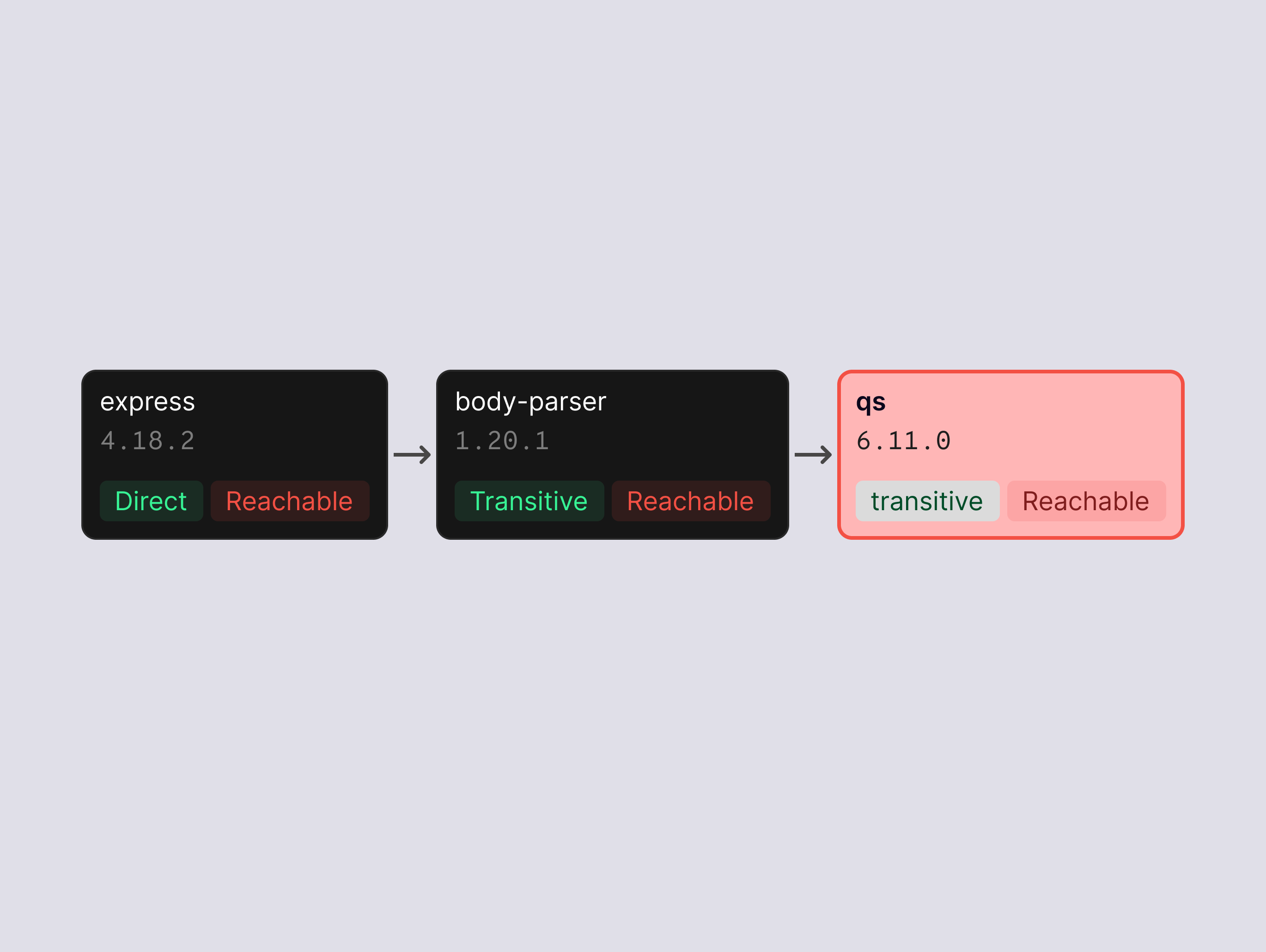
Analyze dependencies in the context of your code
Supply chain scanning runs on the same Component Graph as code scanning, so a vulnerability in a shared library is assessed in the context of every service that imports it.
.png)
Validate exploitability with dynamic testing
Dynamic testing confirms whether a reachable dependency vulnerability can actually be exercised in a running application.
.png)
PR-level scanning
Dependency changes are analyzed for reachability before merge, directly in the pull request workflow.
Unified findings view
Supply chain findings appear alongside code findings in a single queue with the same evidence format and triage workflow.
Prioritized by reachability
Findings are ranked by whether the vulnerable path is actually called by your application, giving your team clearer signal on what to fix first.
Actionable next steps
Each finding includes the reachability verdict, the full dependency path, and upgrade guidance your developers can act on immediately.
Code
Find real vulnerabilities by tracing business logic, data flows, and cross-service interactions across your codebase.
Secrets & sensitive data
Detect and validate credentials across your codebase, CI/CD pipelines, and runtime environments.
Dynamic testing
Confirm which vulnerabilities are exploitable by testing your running application with real attack paths.