depthfirst identifies code paths where specific inputs return authentication tokens or privileged access. These exposures live inside business logic, not configuration files.
Secrets & Sensitive Data
depthfirst identifies credentials and sensitive data by understanding what each value does in your code and systems, validates which secrets are still live, and surfaces real exposures it can remediate.
.png)
-
-
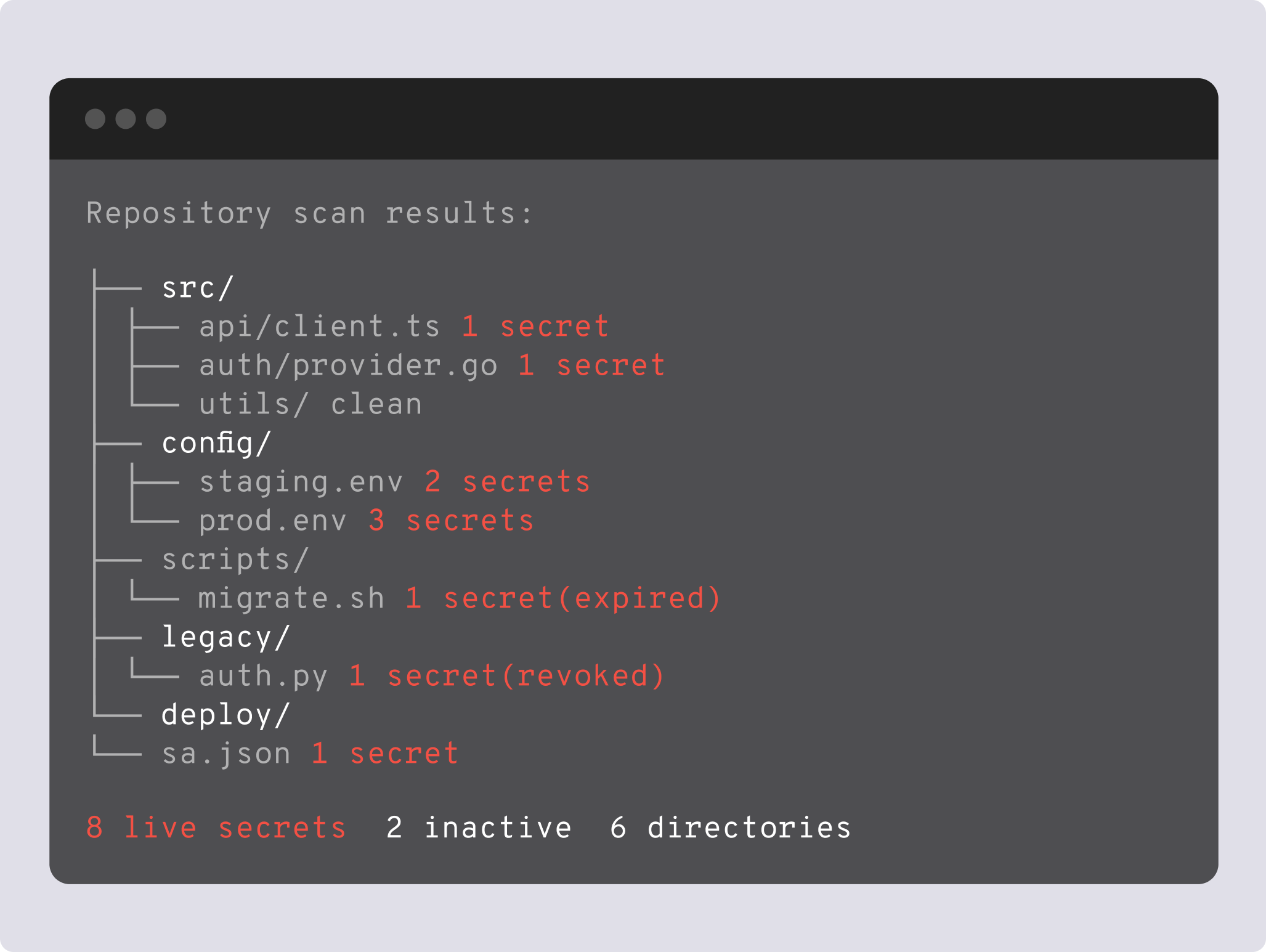
depthfirst scans the full codebase and validates what is still functional. Credentials committed months or years ago that remain live are surfaced with validation status attached, giving your team visibility into long-standing exposures.
-
depthfirst finds personally identifiable information across your codebase and data files, connecting via API or ingesting files directly to surface sensitive data wherever it lives.
Detect Credentials by Context
depthfirst analyzes how your code uses values, how they authenticate, and what access they unlock. It identifies credentials based on their role in the code, not patterns or predefined formats.
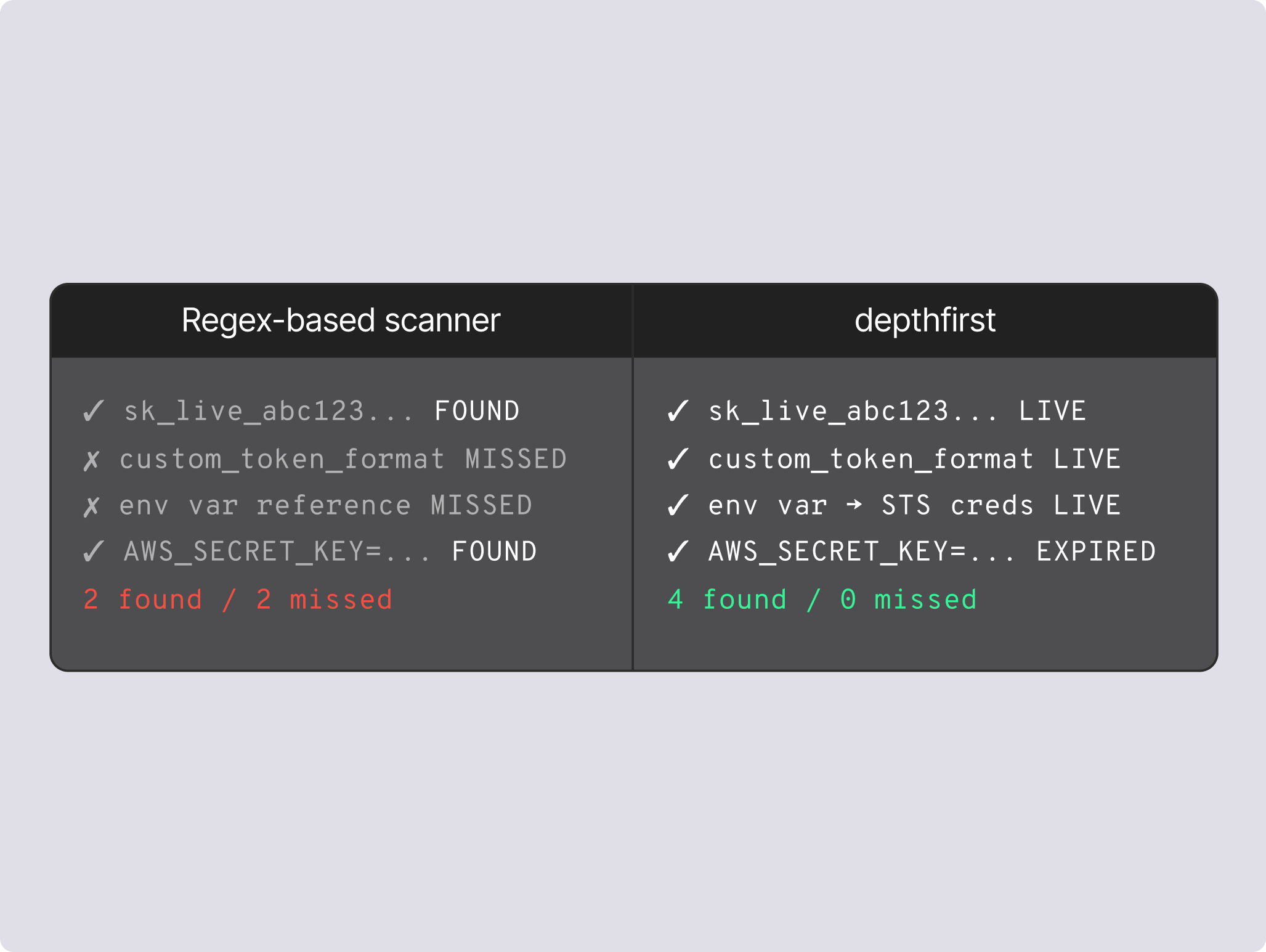
Validate Which Secrets Are Live
Every discovered credential is tested against the service it authenticates to. You see which secrets still work and which ones no longer matter, so your team focuses on real exposures that require action.
.png)
Scan Beyond Your Codebase
depthfirst analyzes your entire codebase including historical commits, and extends to data files and connected systems via API to surface PII and sensitive data wherever it lives.
CI/CD integration
PR scans run in your existing pipeline, flagging new secrets before they reach production.
Source code native
Findings surface as PR comments with one click to view full context and remediation steps.
Deep + PR scans
Deep scans cover the full repo and PR scans catch what is being introduced, all in one tool.
Rotation context
Each finding shows where the secret is used across your codebase, so your team rotates it safely.
Dynamic testing
Confirm which vulnerabilities are exploitable by testing your running application with real attack paths.
Code
Find real vulnerabilities by tracing business logic, data flows, and cross-service interactions across your codebase.
Supply chain
Trace risk through your full dependency tree and surface only the vulnerabilities with a real execution path to them.